See It In Action
A tour through the extension popup — editor, violation tracking, settings, and more.
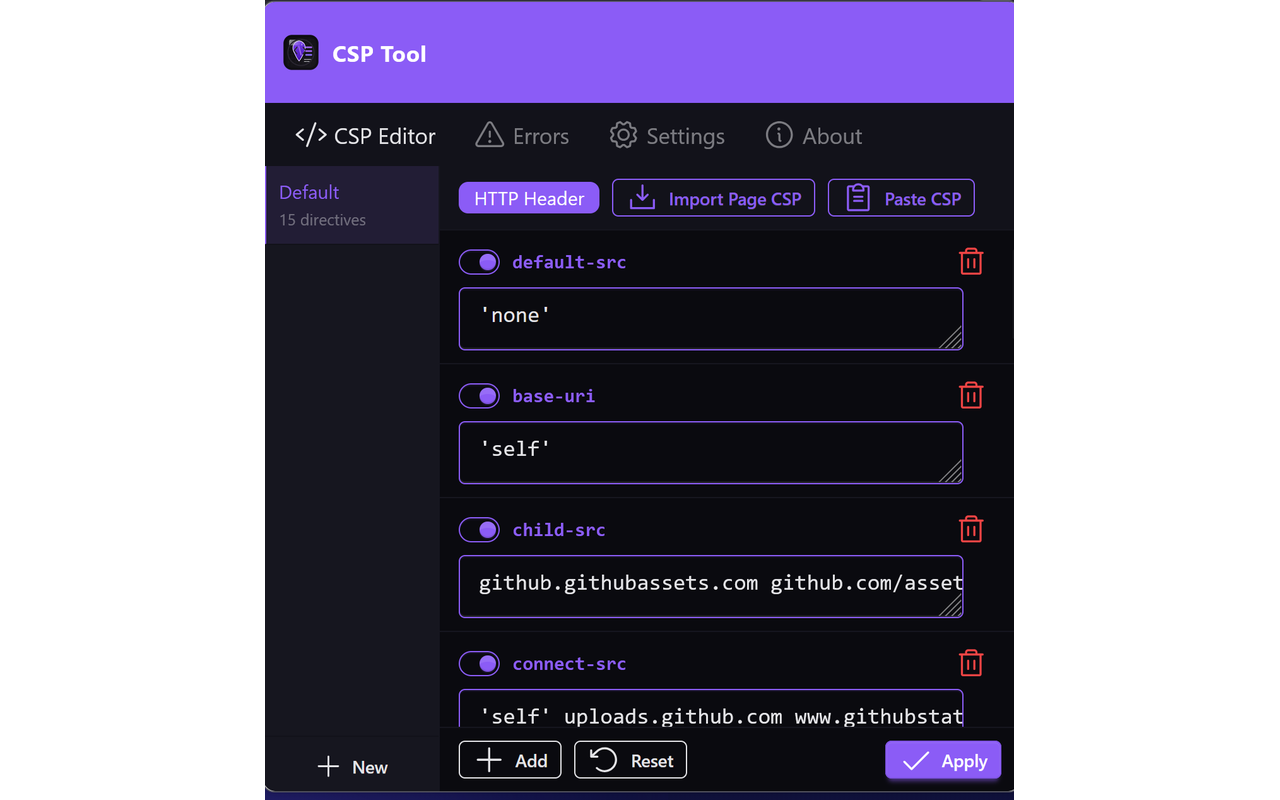
Visual CSP Editor
Browse, toggle, and edit each directive of the active page's Content Security Policy.
Violation Tracking
Watch CSP violations stream in as the page runs, with directives and blocked URIs surfaced in real time.
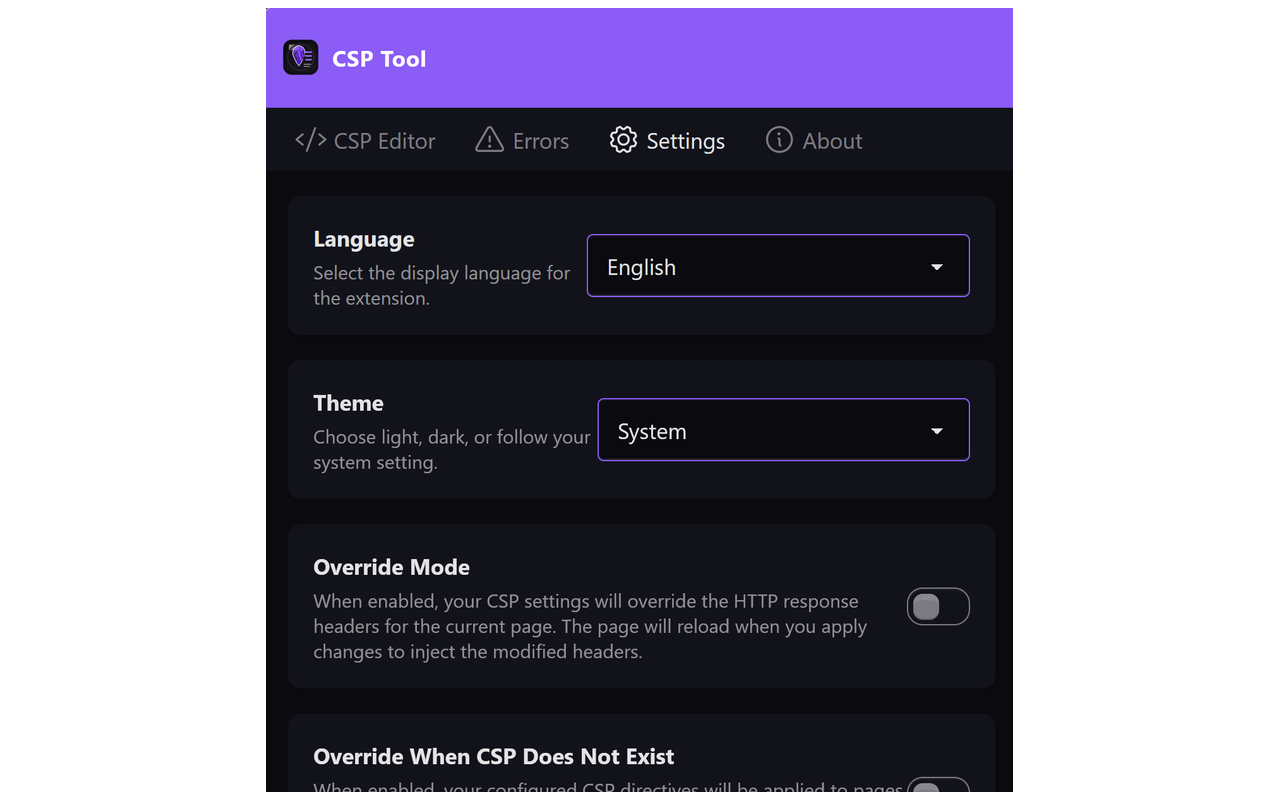
Settings & Modes
Switch between meta-tag and header-override modes, choose a theme, and pick from 15 languages.
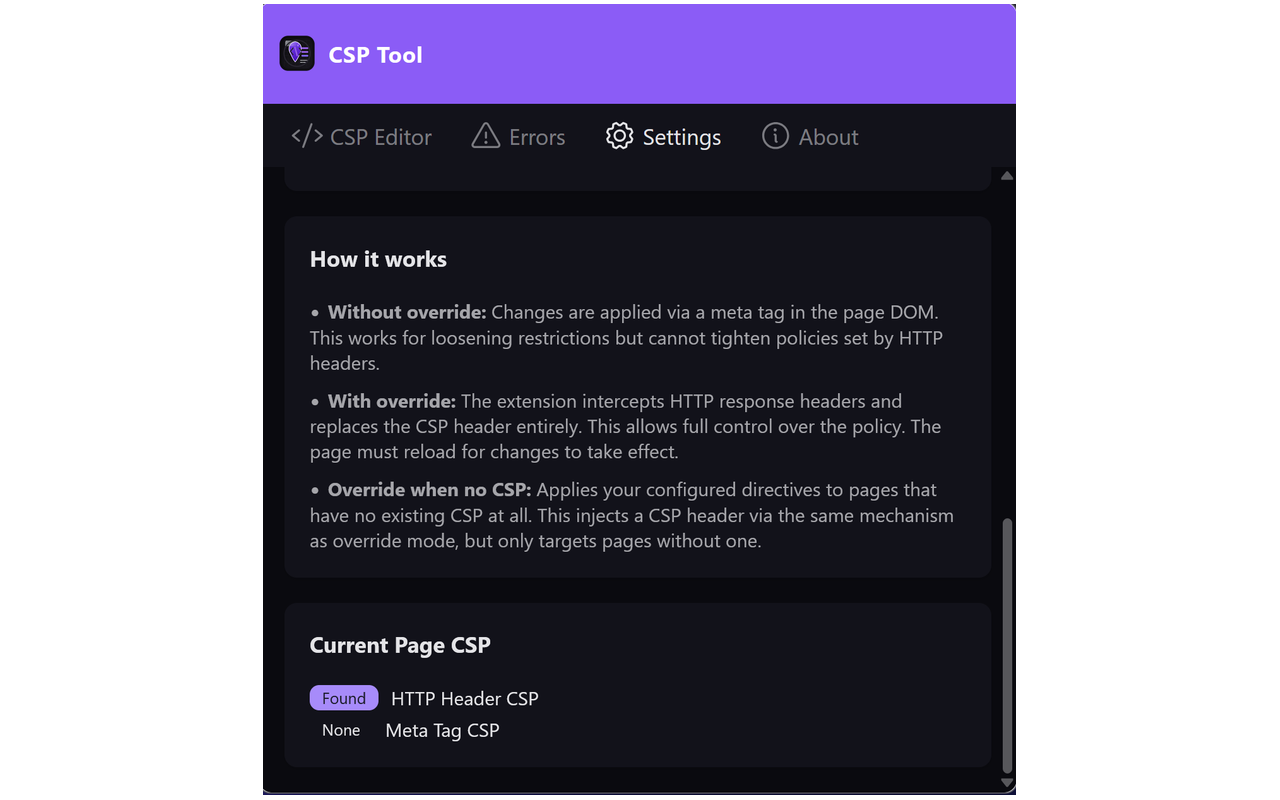
Inline Guidance
Context-aware help explains override modes and shows exactly where each CSP on the page came from.
About & Links
Quick access to documentation, the csptool.net site, and the Aleph Void homepage.